Singapore’s Cybersecurity Frontier: Charting Your Path to Cybersecurity Success

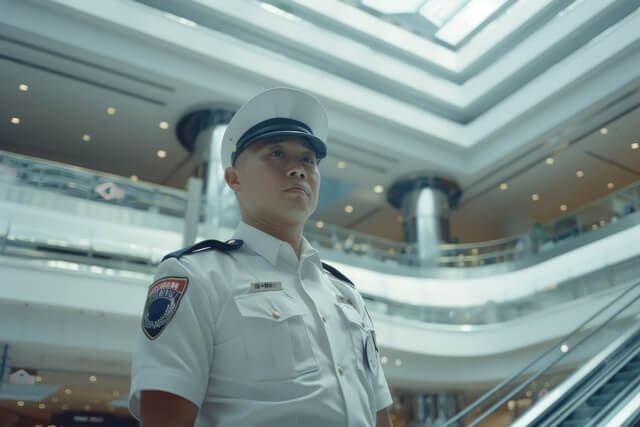
For a long time, security work followed a fairly familiar image characterised by uniforms, patrol routes, guardhouses, and a row of CCTV screens in a quiet monitoring room. That picture still exists, of course. Buildings still need protection, people still need access control, and surveillance remains a big part of everyday operations. But something else […]
Why More Singaporeans Are Choosing Security as a Long-Term Career

A decade ago security work was often viewed as a flexible role that offered opportunities for people at different stages of their careers. It was known to offer valuable experience, provide stability, and create opportunities for those exploring new career directions or bringing wisdom from other industries. Since then, across Singapore, the demand for trained […]
CCTV in the Workplace: Enhancing Security Officer Effectiveness

Walk into any office tower, hospital, warehouse, hotel or retail mall today, and you will find cameras quietly doing their job. They sit above entrances. They line corridors. They monitor loading bays. Most people barely notice them anymore. CCTV in the workplace has become standard. In fact, they are now ubiquitous, and for most people, […]
10 Key Metrics and KPIs for Measuring Security Programme Effectiveness

A security programme can look impressive on paper. Uniforms. SOP manuals. Patrol schedules. Incident forms. But none of that tells you whether it’s actually working. Across Singapore, organisations invest heavily in manpower and compliance. Yet many struggle to answer a straightforward question: Are we performing well or just staying busy? Activity is easy to see. […]
Facility Leader? Why Incident Management Skills Cannot Be Ignored

Facility leaders carry a quiet but heavy responsibility. Buildings may look calm, operations may look smooth, and guests may feel safe, but that sense of order doesn’t happen by chance. It relies on people who know how to respond the moment something shifts. A sudden quarrel. A medical scare. A fire alarm. A confused crowd […]
10 Hidden Dangers of Nightlife Venues and How Security Stops Them, Silently

Nightlife looks effortless from the outside. Music. Movement. Lights. A crowd that wants to enjoy a few hours without stress. But behind that smooth experience are security professionals who carry a quieter responsibility: keeping guests safe without ever interrupting the fun. Many of the risks in bars, clubs, and entertainment venues aren’t obvious to the […]
Life After 50 in Security: How Retirees Are Starting Anew in a New Field

For many Singaporeans, life after 50 feels different—slower in some ways, but richer in perspective. Yet not everyone is ready to hang up their lanyard or stay home. A growing number are taking an unexpected path: stepping into the security industry. They’re finding work that’s steady, practical, and surprisingly fulfilling. It’s a field that values […]
No Time, No Problem: How Security Training Is Adapting to Busy Lives

If you’ve ever tried to squeeze a course into a packed security schedule, you already know the struggle. Rotating shifts, unexpected site calls, and long commutes leave little room for study. After a full day on your feet, opening a textbook isn’t exactly appealing. That reality isn’t lost on KnowledgeTree. For more than 15 years, […]
9 Soft Skills to Skyrocket Your Security Career
If you’ve worked in security long enough, you’ll know this: technical skills get you in the door, soft skills keep you there. They shape how people see you, how teams work with you, and how smoothly a tense day ends. For over 15 years, KnowledgeTree has trained officers across Singapore through WSQ security courses recognised […]
How Hospitality Security Teams Prevent Violence Before It Starts

Most guests at a hotel or event space never think about security. That is, until something goes wrong. But for trained officers, the goal is to make sure nothing ever does. The truth is, the most effective hospitality security teams stop problems before anyone even notices one starting. At KnowledgeTree, we’ve seen how prevention plays […]
